Malware Scanner
Fast & powerful antivirus for your server with infected file cleanup
cPGuard is designed to be a completely automatic defense on your web hosting server against malware with its intelligent threat-detection, symbolic link, binary threats and suspicious pattern recognition.
Advanced Threat Detection Modules
Beyond file scanning, cPGuard extends protection with intelligent modules that actively detect, prevent, and mitigate malware threats across your hosting environment.

AI Scanner - Smarter Malware Detection
Leverages machine learning models to analyze files and detect suspicious patterns often missed by signature-based scanners.

Database Scanner - Scan and Clean Infected Databases
Scans WordPress databases to identify hidden code injections used in phishing, malware distribution, and persistent re-infections..

CMS Threats - Stay Ahead of CVE Exploits
Uses CVE threat intelligence to detect vulnerable plugins, themes, and CMS cores, allowing you to receive alerts or enforce automatic updates to prevent exploitation..
Advanced Firewall Protection
Built with nftables at its core, our firewall is optimized for speed and scalability. Features like temporary bans, port filters, country rules, Dos and SYN flood protection come standard — all in a single, unified system, and minimal overhead.
Learn more →Protection from single-source DoS attacks
Prevent single-source DoS attacks by blocking malicious traffic instantly, keeping your servers safe and running smoothly.
AI enhanced whitelist & false positive removal
Our AI-enhanced whitelist intelligently recognizes trusted sources, ensuring legitimate traffic isn't blocked.
Stop traffic flood from AI bots and crawlers
Effectively block massive traffic floods from AI bots and crawlers using IPDB, ensuring your server stays secure and responsive.
SYN Flood Protection
Block malicious TCP SYN floods while allowing legitimate traffic to pass through, ensuring service remains available even under heavy attack.
Port & protocol filtering
Granular allow/deny rules for TCP, UDP — block or allow traffic by port, direction and protocol to reduce attack surface and enforce service-level access.
GeoIP Blocking
Block traffic from specific countries or regions to reduce attack surface and prevent unauthorized access.
IPDB abusive IP blacklist
A real-time list of IP addresses that have been flagged for engaging in
malicious or
harmful activity like Web attacks, Brute-force, Spamming, DDoS attacks, Port scanning,
Malware
distribution etc.
Learn
more →
Realtime, Collective intelligence
The IP blacklist leverages the strength of attack data from servers, input from our partners and 3rd parties. Our algorithms dynamically generate a real-time list of abusive IPs, scoring them based on various parameters and refining them to prevent false positives. This ensures a smooth experience for legitimate users while actively mitigating potential risks from malicious actors.
Drastically reduce server load
The list acts as a pre-emptive scanner, instantly recognizing known bots, attackers & troublemakers and dropping connection with ipset/iptables at a system level, way before it reaches the web server. This proactive approach helps prevent unauthorized access attempts, DoS attacks, and other malicious activities that could otherwise place a significant burden on server resources.
Web Application Firewall
Our ModSecurity rules are based on intelligence gathered from real-world investigations, penetration tests and research data in the REAL LIFE environment. Our rules specifically designed for PHP applications deliver advanced filtering, security, and intrusion protection.
Optimized ModSecurity rules
Rules for SQL injection, Cross-site scripting (XSS), local and remote file inclusion (RFI), file upload vulnerabilities, zero-day attack, web shell etc.
CMS vulnerability patches and fixes
Protect your WordPress, Joomla, Opencart etc from attacks exploiting the latest vulnerabilities in plugins & themes, XML-RPC attacks and other threats.
Generic Apache & PHP rules
Advanced filtering, security and intrusion protection for PHP sites and applications prevents attackers from exploiting insecure code on shared hosting servers.
Realtime intrusion protection
Our rules act as a shield, actively seeking out and blocking threats before they reach your website, minimizing the risk of damage or compromise
Bruteforce and Bad bot protection
Create a truly integrated server environment where detection, protection, and reporting of security threats happen simultaneously and collaboratively.
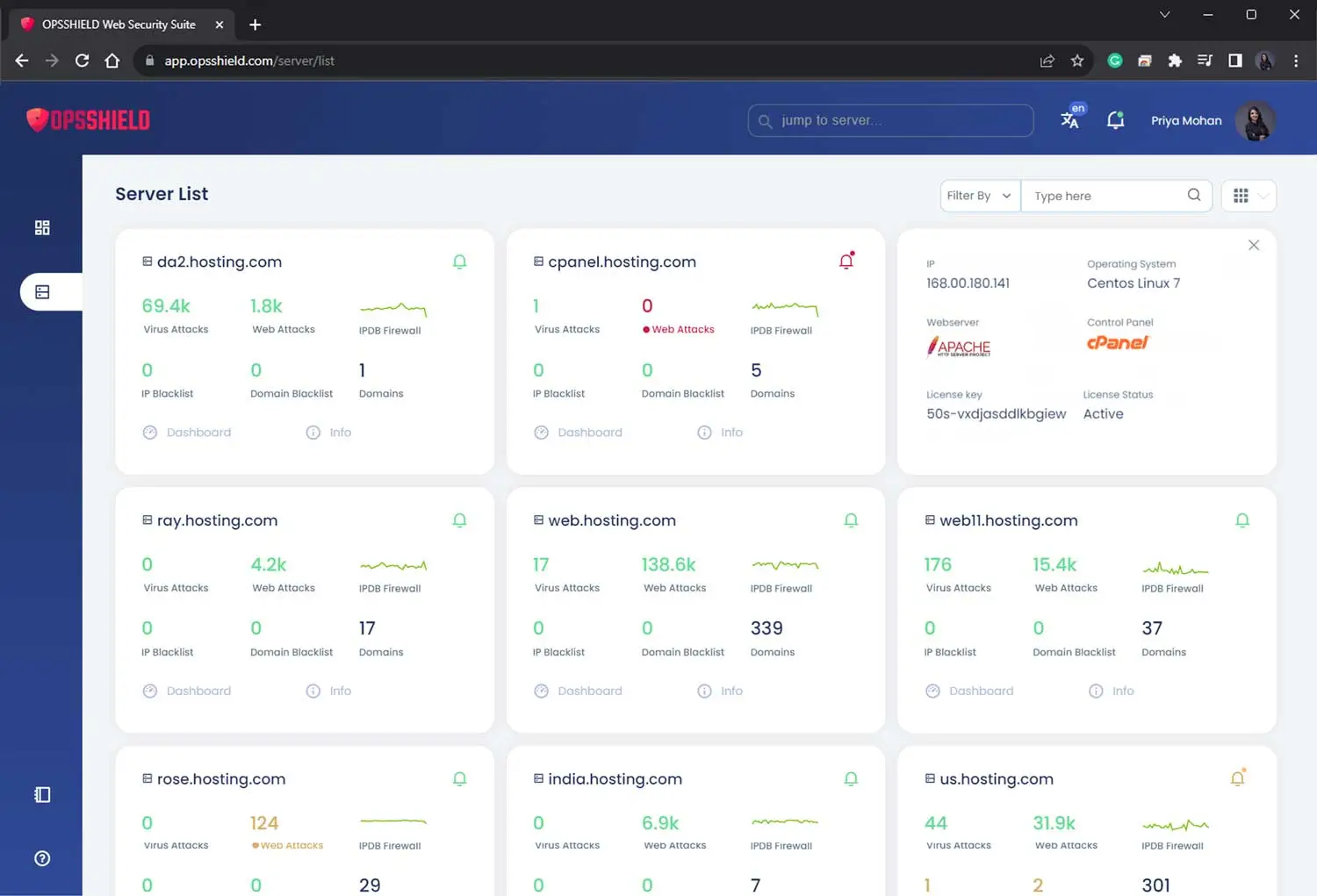
Central dashboard
View and manage all your servers from a single place
Manage all your servers from a single interface, easily switch between servers, view server details, reports, events, change settings & do bulk actions. Easily add & share the server with other users.
Feature-rich Command Line Interface
Our command line interface (CLI) unlocks a deeper level of control to advanced users. It provides several helpful commands that enable you to use and configure cPGuard even without a user interface.
Try cpgcli --help on your server with cPGuard.
Quick and painless setup on all major control panels
You can deploy cPGuard in minutes through automated scripts, seamlessly integrating with popular platforms like cPanel, Plesk, and DirectAdmin, Enhance, Runcloud etc.
Puts you in control by offering support for all major Linux distributions, empowering you to choose the perfect fit.






Other features
Uncover the full spectrum of features within cPGuard
Automatic account suspension
Immediate suspension upon reaching a set threat detection criteria minimizes potential damage from viruses or blacklisted domains, protects sensitive data, prevents malware propagation and full server compromise.
Block requests by countries
Incoming requests from specific countries or regions can be either allowed or denied based on your settings.
SRBL mail server RBL
Automatic spam filtering saves time and resources by preventing spam from reaching your mail server and consuming processing power.
Spam monitoring
Monitors and reports potential spamming scripts by analyzing mail queues.
Process monitoring
Continually observes active processes, identifying and mitigating potential threats such as malware and resource-hogging crypto-mining scripts in real time.
WordPress wp-cron scheduling
Optimize the execution of wp-cron, ensuring efficient background processing, optimal resource usage and reduced overload during peak hours.
CMS core file replacement
Automatically replace infected core files of popular CMS and plugins with clean, original versions from our CDN.
Block PHP file upload
Implement proper file upload security measures by blocking PHP script uploads via forms in insecure code.
WordPress core file integrity checks
Regularly verifying the integrity of critical files in a WordPress installation without manual intervention. This security measure helps ensure that core files have not been tampered with or compromised, reducing website downtime.
Daily security and alerts report
A daily security digest is a valuable tool for staying informed, proactive, and in control of your system's security. By regularly reviewing these reports, you can make informed decisions, prioritize security efforts, and ensure a safer and more secure environment for your server.
Daily scan
Ensure no file is left unchecked by automatically rechecking files modified in the last 24 hours.
Weekly scan
Systematically reviews and rechecks files modified within the past week on a system or website.